Category: Blog
Sage 200C & Cash Flow Enquiry
By Darren Posnack
28/04/2020
Sage 200C & Cash Flow Enquiry
For most businesses in the current climate keeping control of cash flow is a major priority.
Sage 200c has a user-friendly Cash Flow Enquiry as part of its Cashbook Module, which can help you maintain visibility and manage cash flow easily.
The cash flow structure pulls information from bank accounts, sales ledger, purchase ledger, sales, and purchase orders, nominal budgets and manual ad-hoc income and expenditure entries, VAT due/to claim, Contracts from Sicon Contracts and Applications and Retentions from Sicon Construction.
You can use the simple drag and drop feature to adjust the transactions in the cash flow interface to reflect the expected cash impact without changing the due dates and promised dates manually.
Features include:
-
Select the period you wish to view
-
Select the Bank accounts to be included
-
Transactions types to include: Regular Receipts/ Payments (Standing Orders & Direct Debits set up in Sage)
-
Forecast Receipts/ Payments (Sales Ledger & Purchase Ledger items based on Due Date)
-
Manually remove transactions you know you will not be paying or receiving in the current period
-
Manually add additional Receipts/Payments
This link to the ‘Sage 200c help files’ provides more detail:
In addition to this, you may also be interested in a new add-on module for Credit Control. The Roundhouse Credit Manager module links directly to the Sales Ledger and has the look and feel of the standard Sage List View screens.
Features include:
-
The Age of the Debt
-
Whether they have orders to be processed
-
Where orders have been placed on hold
-
Keep notes on chases that have been made
-
Produce letters to selected accounts
-
Place accounts on Hold from the Credit Manager screen
Filter lists of customers based on:
The following link – Roundhouse Credit Manager provides a bit more information.
If you are a Sage 50 Accounts user, there is a Cash Flow module, as well as other options for Credit Control. If you would like more information about these modules, Cash Flow Enquiry or The Roundhouse Credit Manager please contact service@utilize.co.uk today.
Learn more about Finance management85% of businesses with less than 1000 employees have been hacked … and most don’t even know it!
By Darren Bartlett
02/04/2020
Reports of cyber attacks originating from the Dark Web are growing at an alarming rate. The attacks are becoming more frequent and increasingly harder to detect.
Hackers who initially compromise a network can be in the network for months, and sometimes even years, before their activity is spotted. It is more rewarding for them to compromise further systems and identify additional criminal opportunities to sell these vulnerabilities, passwords and hacks on to other criminals to exploit.
Alongside selling hacking tools, there are hackers for hire who are paid specifically to compromise a specific company’s networks. Data gained illicitly from your company may already be available in Dark Web data dumps, or from criminals selling data such as your employees personal records, compromised passwords, or system access exploits.
“48% of UK Businesses identified at least one breach or attack a month”
Although many businesses believe they are relatively ‘secure’ from cyber attacks and cyber security in larger businesses is generally improving, cyber attacks on medium and small business are increasing in number and frequency.
These attacks can start with the compromise of a single employee’s login details through a basic phishing attack. With one in every 3,722 emails in the UK being a phishing attempt, and a 350% surge in attacks amid the COVID-19 epidemic, your company cannot afford to ignore the threat of a potential data breach.
You must begin to mitigate your risks and take proactive steps to identify whether your businesses data has already been compromised and protect against the possibility of a future attack.
Read our Free Guide and discover the necessary steps your business should be taking.
Learn about Managed SecuritySpear-Phishing, Social Engineering & Email Attacks. Why prevention is better than cure!
By Anna Gonzalez
27/03/2022
Spear-Phishing, Social Engineering & Email Attacks. Why prevention is better than cure!
Email attacks, phishing, insider threats, and spoofing have all spiked recently, and these increasingly sophisticated attempts to access your data and personal information are leaving widespread disruption in their wake.
Last year, 32% of businesses and 22% of charities in the UK reported having experienced cybersecurity breaches or attacks within the previous 12 months. The most common types were phishing attacks (identified by 80% of these businesses and 81% of these charities). Many also reported cases of others impersonating an organisation in emails or online (28% of these businesses and 20% of these charities) as well as viruses, spyware and malware attacks.
The nature of these threats
Cyber-attack victims are not necessarily selected at random; many are systematically targeted in order to infiltrate systems. Pen testing tools such as MimiKatz are used to search for the individual credentials of users with domain admin privileges, so that these accounts can proceed to spread malware more effectively. This method is typically behind the largest and most advanced ransomware attacks and breaches, with SOPHOS recently publishing that 54% of businesses have experienced a rise in this method of attack.
Email-based spoofing has also increased, as attackers employ ever more sophisticated methods in their attempts to gain access to money, intellectual property and other credentials. The most common attacks are initially aimed at C-level personnel, before spreading to other members of staff within the organisation. Mimecast’s 2019 report found that this sort of malicious activity from one employee to another could account for as much as 73% of individuals experiencing direct loss of data, finance or brand.
Smartphones today are minicomputers containing a large amount of sensitive information about our lives, including banking details, maps, our health, where we live and where we run. So, it may come as no surprise that 2019 also saw a growth in mobile attacks. Google Play and Apple are getting better at scanning applications, but cybercriminals excel at tweaking their plagiarised applications to avoid detection. When installing little-known applications, always remain vigilant for any small print in ‘free’ trials that require laborious steps to uninstall or unsubscribe. Failure to do so on some apps can result in hundreds of pounds in ongoing monthly payments.
Apps designed to steal credentials for online banking have plagued Android users for some time with malicious code not downloaded until after a user downloads the app – making it more difficult for Google to scan and detect. The malicious code then monitors your actions and keystrokes on virtual keyboards when logging into your banking app.
With the advent of GDPR, protecting our business and personal data has never been more important. So, as phishing, spoofing and spear-phishing increase, businesses must also urgently tackle the biggest risk to their organisation – their users. Yes, human error is a major contributing factor in breaches, which is why many companies undertake internal phishing simulation exercises with employees to evaluate their vulnerabilities. The results are often alarming.
But fear not, there is good news too. Educating employees and nurturing a culture of vigilance and awareness, through the consistent delivery of fresh and engaging training, can make a real difference and arm businesses with an additional line of defence.
Where to focus your resources
In the face of these every-changing threats, some of the old preventative measures can still provide the most effective protection. But there are some new recommendations and technologies to add into the mix too…
Patching
Many of us will have heard of Patch Tuesday, but not everyone places the same value on patch management. It can be a lengthy and laborious task but having a process in place for this is vital – either internally or via your IT support company.
Multi Factor Identification
MFA – or Multi Factor Authentication means having a separate token or device to confirm your user identity. MFA can take the form of an authentication app (such as Microsoft Authenticator) or Authy, which once paired with an individual’s account, provides a sequence of numbers every 30 seconds. The important part is that this is on a separate device to the one you are using – such as your phone. You should set up MFA on any application that supports it but particularly those with access to sensitive information.
Passwords
It is important to use strong passwords and for users to understand their importance. Passwords should not be reused, and this is particularly important for business passwords (or email/password combinations). Wherever possible, consider using an accredited password manager such as Last Pass, 1 Password or Dashlane. Click here to find out more
Awareness
If your users understand the importance of data privacy and the value of their personal information, they are more likely to look after the keys to your network. Fostering an open environment, where employees feel able to discuss possible phishing attempts and questionable emails or calls without the fear of reprimands, is an excellent start. Utilising a continual education platform is even better.
Accreditations and scanning
Cyber Essentials Plus, ISO27001, PCI DSS are great accreditations for your business to acquire and they show your suppliers and customers that you are serious about security. These accreditations align with GDPR and other requirements such as internal and external scanning. If accreditation is not feasible then a vulnerability scan should be considered as a regular addition as many exploits or breaches lie undetected for up to 6 months. Know the vulnerabilities within your business so you can work to bolster them. Understanding your systems, how they are connected, and the associated risk management, all play a vital role. Depending on your size, you may even want to consider walking through your ‘playbook’ – does everyone in your business know what to do if a breach/hack/disaster happens? This includes understanding how to approach the ICO in the worst-case scenario.
During these challenging times, we are experiencing a spike in cyber-attacks with many themed around coronavirus and the associated government/HMRC advice. As our workforces continue to adapt to remote working and a ‘new normal’, it has never been more important to be vigilant and ensure some of the simple precautions and best practices outlined above are implemented across your organisation.
Learn about Managed SecurityCyber criminals are becoming more sophisticated and attacks more frequent!
By Darren Bartlett
19/03/2020
Cyber criminals are becoming more sophisticated and attacks more frequent!
Undoubtably you’ve heard mention of the Dark Web – a network of website and servers that
use encryption to obscure traffic and hide exactly who is accessing their content. Because the
tools you need to access the Dark Web are designed to give you anonymity, it has become a
hotbed of criminal activity, used to sell drugs, pornography, weapons and more recently stolen
data.
But why should your business care about the Dark Web, what appears there and how could it
effect your organisations security?
Cyber criminals and cyber attacks are not only becoming more prevalent, with 88% of UK
Business suffering a breach in the last 12 months, but more sophisticated and therefore more
harmful. Hackers who initially compromise a network can be in the network for months, and
sometimes even years, before their activity is spotted.
In fact, Data gained illicitly from your company may already be available in Dark Web data
dumps, or from criminals selling data such as your employees personal records, compromised
passwords, or system access exploits.
Digital credentials, such as usernames and passwords, connect you and your employees to
critical business applications, as well as online services. Unfortunately, criminals know this,
thats why digital credentials are among the most valuable assets found on the Dark Web.
Microsoft sees over 10 million username/password pair attacks every day.
You can’t afford to ignore the Dark Web. Your business needs to take proactive steps to monitor
the Dark Web for employee credentials, insider threats, customer accounts for sale,
compromised banking information, and criminal discussions requesting targeted resource
development focused on compromising your business.
Discover the necessary steps your business should be taking, Read our FREE essential guide.
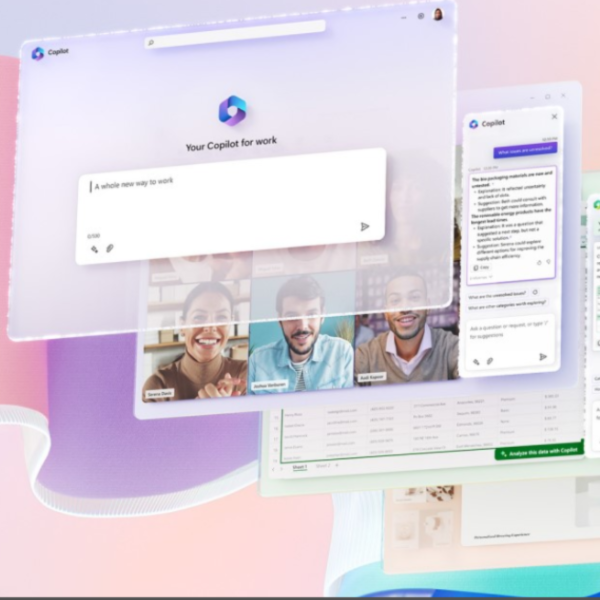
Learn about Managed SecurityBoost your Business with Microsoft Teams
By Rob Ward
26/02/2020
Boost your Business with Microsoft Teams
We can be contacted in countless ways – by phone, mobile, text message, email and in person – to agree deadlines or set up meetings. It takes time to go to your calendar to input reminders or meeting dates and it’s all too easy to forget to do it or overlook an invitation from a team member to a critical meeting.
With the introduction of Microsoft Teams comes a number of solutions to help combat business communication, organisation and administrative issues. Automation of your calendar can pick out key dates from every communication tool, including chat, documents and video/voice calls, and create calendar reminders.
You no longer need to do this manually! Not only do these important dates appear in your calendar, they are automatically shared with all relevant stakeholders – saving time and increasing productivity. Everyone knows what is expected and by when.
Microsoft Teams breaks down silos and brings people together from anywhere, anytime, and on any device. Not only does this improve collaboration, it increases job satisfaction by reducing stressful encounters and increasing a sense of achievement. It’s also fun to use – which means users are inclined to use it more frequently and consequently work more productively!
“Successful businesses understand the need to continuously improve their business processes and supporting tools: to become more efficient and productive, and to respond to market changes faster while providing better service to customers.” -Entrepreneur
To put this into context, take a look at just a few examples of how Microsoft Teams can help overcome the business challenges you face on a daily basis.
A fun feature within Microsoft Teams is the “like” emoji that quickly acknowledges that an email or chat message has been received and the information within it is acceptable. That’s one less email to read, and it’s a fast and fun way of agreeing to a suggestion or idea. We do this in text messages – how useful that we can use it at work too!
OUT OF TOUCH WITH COLLEAGUES, UNSURE WHO IS AVAILABLE?
Microsoft Teams puts all of the communication tools you need in one place. You have total visibility on who is available for a quick instant message, a chat, video or voice call.
WASTING TIME PICKING OUT KEY INFORMATION FROM THE FLOOD OF DAILY EMAILS AND MESSAGES?
Whether it is in a chat, file or threaded conversation, you’ll find exactly what you’re looking for in one place – your relevant Microsoft Teams channel. You can also bookmark a conversation or even save specific parts of one. Microsoft Teams makes it quick and easy to track down the important project specific information you need.
LOSING VALUABLE TIME SWITCHING BETWEEN DIFFERENT APPLICATIONS AND TABS?
Microsoft Teams allows you to access all your files, apps, conversations and important business processes from with a single secure space.
MEETINGS ROOMS BOOKED, CAN’T FIND A PLACE TO CARRY OUT YOUR CONFERENCE CALL?
With Microsoft Teams you can meet from almost anywhere with full audio, video and chat. With blur my background, you can even eliminate distractions from the periphery so you can ensure that your team or clients remain focused on you.
STRUGGLING TO WADE THROUGH TOO MANY MESSAGES, JUST IDENTIFY THE ONES IMPORTANT TO YOU?
With Microsoft Teams you can filter your messages to easily identify the most critical to you. Just go to the Microsoft Teams Activity feed, select the funnel icon and filter for @mentions or responses to a message you sent.
Yes, businesses can (and do) collaborate without Microsoft Teams. They use emails, meetings, file sharing services – even Post-it Notes! The problem with these traditional methods is that even though they can offer instantaneous communication, they aren’t always visible to all stakeholders – it’s easy to forget to add someone to a distribution list or miss out on valuable input because a person is out of the office. Meeting space, travel and video facilities are additional costs and it takes time to physically move between offices for a meeting or to track down the person you need and, on the way, there is the potential for distraction. Digital collaboration is vastly different as it can securely connect internal users and external partners – allowing them to accomplish much more, in a more timely manner.
Discover how the introduction of Microsoft Teams can improve communication and productivity in your business.
View our Communication offeringsStop, check and check again
By David Tuck
07/01/2020
It seems every day we are hearing about the latest loss of data, how companies and individuals have been “tricked” into handing over large sums of money and how our personal information is being used without our knowledge.
I am sure that many of these things have always happened, confidence tricksters and “con artists” have been with us for a long time, so why is it happening more frequently now?
Technology has indeed made it easier to communicate and move information around, but unfortunately, this makes it easier for the fraudsters too.
Over the last few months, I have seen a growing number of organisations caught out by such fraudsters. These tend to be smaller businesses where staff know the CEO or Owner and are used to taking informal instruction from them and do not question too much when this happens.
So, what can we do to combat this? One piece of advice I can give is to take an “old fashioned” approach.
This may seem at odds with today’s fast-paced world of technological marvel, but just think, in the past did shops give you something essentially on the promise that you would pay? It would have been interesting to go into a shop and tell the staff that their Manager before going on holiday, said that it would be okay for you to pick up the latest TV for free whilst they were away. And just to prove it, you have an unsigned letter with their name on it. I suspect you would have been politely asked to leave!
Adopting an “old fashioned” approach is one way to combat this. Don’t give anything to anyone until you have spoken to the person who has authorized it, either face to face or on the phone (and of course, you ring them, not vice versa). Always be suspicious if the authorizing person is conveniently on holiday or not in the office.
Be “old fashioned”, take your time, check and do not be hurried into making a decision. If the person doing the asking in the email is really your CEO, they should appreciate your thoroughness.
And if you are the CEO and have just received a quick phone call from your accounts person while you lie on the beach in the Bahamas, don’t be upset with them for double-checking. That few minutes of your time could probably be the best investment you have ever made. After all, where can you save £100,000 by taking a 2-minute call today?
Contact UtilizeCyber Essentials - Why it's like locking your car!
By David Tuck
16/12/2019
Unfortunately, it’s a sad fact that smaller companies are more likely to fall victim to cyber criminals than larger ones. You may think that because you don’t have a high turnover or a prominent public profile that you can escape detection from cyber criminals, but don’t be fooled. Criminals know that larger companies have significant security resources, thus making circumvention of these defenses much harder and this challenge often acts as a deterrent.
If they do manage to break-in, the payback may be substantial, but so is the risk. Spending three months trying to hack into an organization takes significant investment from a hacker and the risk of detection will grow each day. A large company is far more likely to report a breach to the authorities and try to recover its lost data or money.
Often it is easier to target 50 small companies, where the risk of detection is minimal. These small companies won’t have the skills or the resources to put in place complex defenses and 50 small targets can often be more valuable than one large one.
I often hear “well the hacker will get in anyway, won’t they? So why bother spending all this money when it won’t do any good!” A well-resourced hacker or sovereign state with limitless resources will indeed get in, but this is not what you are trying to defend against. Making your company less palatable, is the goal you want to achieve.
Most hacks, like thefts, are opportune. The hacker will scan thousands of IP addresses until they find a vulnerable one and then exploit it. They may even be in your system for months or years, gathering information before you are aware of it. On average, it takes 177 days for a break in to be detected, for every threat that is detected quickly, there are far more that are not. Your company could have been breached in January and you may not even be aware yet!
So, what can you do?
Well, you wouldn’t leave your car unlocked in the street, would you? Yes, we all know that if someone wants to steal it they will. You lock it to prevent the opportune thief and that is what you need to do with your IT systems.
If you’re not a cyber security expert, where do you start?
Luckily you don’t have to be an expert to make a difference. Schemes such as Cyber Essentials and Cyber Essentials Plus address the most common themes. Think of these as mini-audits of your IT systems against the most common ways hackers get in. If you carry out a Cyber Essentials certification, you will address 80% of the most common vulnerabilities in IT systems today. This may not be 100% foolproof, but it goes a long way in helping you to deter that opportune hacker, encouraging them to move on to the next easier target, the next car in the street.
So lock your car – show clients and hackers that your company takes information security seriously. Complete Cyber Essentials/Essentials Plus and help to secure your IT systems from attack
We’ve written a short guide to help you better understand Cyber Essentials Certification and how it can benefit your organisation.
Contact Utilize10 top tips for the perfect technology support partner
By Rob Ward
24/06/2019
Before you take on a new employee, you interview them to find out about their experience and motivations. Employing a Technology Support Partner is no different – you need to find out about their business principles, working practices and other commitments before you make a decision to work with them. To do this, we recommend asking a series of questions which allow them to share openly and honestly with you.
Questions that elucidate, for example, about their specific industry experience and how they explain technology requirements to you, Let’s face it, for most of us, tech talk is a foreign language which needs to be translated into plain English – it’s imperative that you start these productive conversations before you make any commitments.
As well as being sensible, it’s important to remember that any Technology Support Partner will have access to all of your internal systems and data and, as well as the trust issues, they will play an integral role in your future business success.
To help SMEs have these very important conversations, we have compiled 10 top tips: questions that will help you ascertain if your prospective tech partner is the right fit for your business.
Read our full blog here and get talking. Employ the wrong partner and it could cost you dearly. Get it right and it will propel your business forward.
Contact UtilizeUtilize: Disability Confident Committed
By Guy Hocking
11/04/2019
Utilize: Disability Confident Committed
As part of our ‘People First’ initiative, we’re proud to announce that we have recently gained the accreditation of Disability Confident Committed marking the first steps on our path to becoming a full Disability Confident Employer.
I’m sure you share our vision for a society in which disabled people and those with health conditions can work in good jobs to fulfill their full potential. The fact that 83% of people will acquire a disability whilst in work probably indicates we are already working alongside colleagues who could maybe benefit from some extra help or support.
The Disability Confident scheme helps organisations like ours with the skills and confidence needed to recruit, retain and develop disabled people who bring commitment and energy to an organisation.
We intend on launching a series of Cloud Workshops showcasing the hidden and often untapped features within the Microsoft portfolio specifically designed to help people with accessibility problems.
As a Disability Confident Committed Employer, we have committed to:
- Ensure our recruitment process is inclusive and accessible
- Communicate vacancies and offer interviews to disabled people
- Anticipating and providing reasonable adjustments as required
- Supporting any existing employee who acquires a disability or long-term health condition,
enabling them to stay in work - Promoting at least one activity that will make a difference for disabled people
Please look out for details of our forthcoming workshops and progress updates on our Disability Confident journey.

Lack of Multi-Factor authentication is helping criminals access your data
By Rob Ward
11/12/2018
Lack of Multi-Factor authentication is helping criminals access your data
The lack of multi-factor authentication helped criminals to steal usernames, email addresses, social media tokens and 4.7 million phone numbers from 21 million users of social media app Timehop. The app, based in the cloud, resurfaces old photos and posts by connecting to your social media profiles. “Access tokens”, which are allocated to Timehop by social media providers, were also taken and could allow criminals to view a range of social media posts without permission.
Multi-factor authentication is the process of confirming your identity in two different ways before access is granted to an account or service, such as a PIN or password, a secondary device such a key fob or card reader, or via biometric data such as a fingerprint. We recommend that all our clients implement a multi-factor authentication process to help protect they IT systems and data.
Learn about Managed Security